Defeating The Virus Mac OS
It was once a widely held belief among Apple enthusiasts that macOS (or OSX as it was then known) was a far more secure system than its Windows or Linux counterparts. Malware outbreaks were rarely heard of, and most legacy AV solutions were known more for their high rate of false positives and greedy consumption of resources than they were for preventing any real adversaries. Asked “do you really need antivirus software for macOS”? about the only reason Mac users would say “yes” would be to catch Windows-based malware in email attachments. Why? In the words of this forum poster, as a public service to the unfortunate!
macOS Security By Design?
All that began to change from 2011 onwards, a fact reflected by Apple’s increasing hardening of the OS. In every release of macOS since then, we’ve seen the introduction of more security technologies and a locking down of the system: Gatekeeper, codesigning, Xprotect, Malware Removal Tools and more. With the release of macOS Mojave this year, Apple once again introduced new security features in response to the evolving threatscape facing the platform, restricting Apple Events and hardening user data protections.
Apple, of course, should be commended for taking security seriously, something even they are aware that their users often do not. Apple says that macOS “provides security by design” and
includes the key security technologies that an IT professional needs to protect corporate data and integrate within secure enterprise networking environments
(The Safe Mac also has an excellent website and Twitter feed if you want the latest, up-to-date info on Mac Adware, Malware, and security concerns.) One click in Adware Medic can cure all that.
- Effectively Get Rid of CaptchaReverse.com Push Notification Virus (Windows OS and Mac OS) 2021-04-16 Sarah. CaptchaReverse.com Push Notification Virus. CaptchaReverse.com Push Notification Virus is considered as a hijack virus by potentially unwanted program (PUP) that comes into your PC with the third party application by method of package.
- All it takes is one thoughtless click on a link in an email or on a website, and your Mac could be infected. The good news is that performing a Mac virus scan is very easy and if it finds anything, getting rid of the virus is very straightforward, too. How to check your Mac for a virus. There are a number of tell-tale signs that your Mac has a.
- 10 Step Mac tutorial on how to remove ALL viruses, malware, adware, spyware, and basic Mac maintenance and cleaning 2019Try a new and improved browser built.
The company are proud of their security posture, and are keen for customers to feel reassured that safety is a top concern:
macOS system security is designed so that both software and hardware are secure across all core components of every Mac. This architecture is central to security in macOS, and never gets in the way of device usability.
Fantastic. It’s just what you want to hear from your OS vendor.
Except, it’s all a bit of a myth.
As it turns out, malware can easily defeat macOS security protections. Let’s take a quick look at the main reasons why relying solely on Apple’s built-in protections is dangerous for your business.
Application Security
You’ve probably got Gatekeeper turned on even if you don’t know it. It comes enabled by default to allow you to download and run applications that are either from Apple’s App Store or Identified Developers (in other words, developers who are part of Apple’s Developer program).
Gatekeeper is great, except for one thing: it’s only protecting one gate: downloads that come in through GUI apps like Safari, Mail and so on. But there’s a few other gates that malware can use that Gatekeeper is blind to, like curl, ssh, and package managers such as brew. Download something through these channels, and Gatekeeper will never know. Note line 13 in this typical adware installer script, which bypasses Gatekeeper with ease:
How To Check For Virus On Mac
You have likely heard of XProtect, and some may think that XProtect will plug the holes left open by Gatekeeper, but that’s not the case. XProtect relies on Gatekeeper to tag downloads with a special attribute or “quarantine bit” which effectively says to XProtect: “be sure to check this against your malware signatures”. Without that attribute, XProtect doesn’t kick in. What’s worse, even software that is tagged with this special quarantine bit can be unquarantined by any other process without elevated permissions. In short, one piece of malware can let in any other piece of malware, too. Even if Apple have revoked a rogue Developer ID, such as occurs when malware strikes from the App Store, removing the quarantine bit will still allow that malware to run.
And then there’s the paucity of XProtect’s “Yara” based rules. At last count, XProtect had less than 100 malware signatures. Although there was a minor bump in October of 2018, it hasn’t had a significant update since March 2018.
There’s also the transparency of XProtect’s “Yara” based rules. Any malware author can see exactly how Apple are detecting their binary and change it accordingly, so the rules can become invalid as soon as they are pushed out to users.
There’s a third level of App Security built-in to macOS that is not so widely known called MRT, the Malware Removal Tool. According to Apple, in the event that malware should
make its way onto a Mac, macOS also includes technology to remediate infections
New Mac Virus
But there’s two problems with Apple’s malware removal tool which make malware unafraid of it: first, it’s based on hard-coded paths, and most malware will use random or changing path names; second, it only runs once each boot.

By that time, a malware infection may have come and gone, taking your data with it, or encrypting it and leaving you a nice ransom note.
Access Control
Central to access control on modern Macs is System Integrity Protection or “SIP”, aka “rootless”, which prevents malware from attacking system files. SIP is enabled by default, and it means that even the root user cannot modify or delete any files under its protection. In macOS Mojave, SIP can even be extended to 3rd party apps if they opt-in to the new hardened runtime.
SIP is an essential technology, but SIP bypasses are not unknown. It’s also worth noting that if you have legacy AV software that simply whitelists everything in the /System/Library folder, you could be in for a shock, since not everything in there is actually protected by SIP. The following are all excluded from “rootless” protection:
Another core aspect of access control is kernel security. As Apple have themselves noted, kernel security is essential to the security of the entire operating system. Unfortunately, their recognition of that is undermined by the fact that any unprivileged user can approve installing new kernel extensions. Combined with security holes that allow processes to simulate user clicks, therein lies an open door for malware. Apple have made several attempts to lock down simulated user clicking in the past, only for new 0day exploits to appear that have bypassed them.
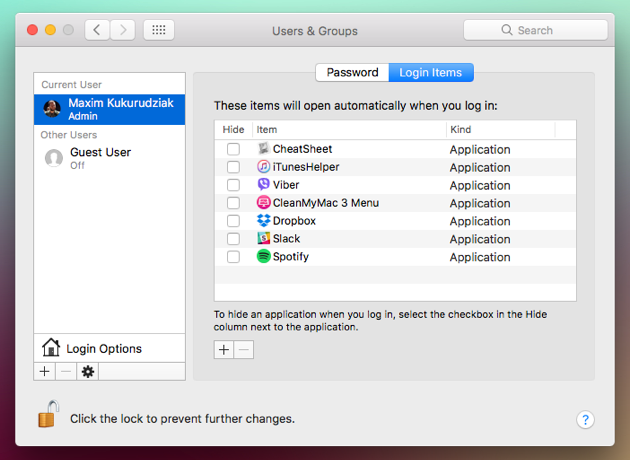
If you’re using a Mac that’s enrolled in Apple’s Device Enrollment Program, you will be familiar with MDM and Config profiles as a means of controlling access to applications, services and preferences. Malware authors are also aware of them, and have taken to slipping managed preferences onto user’s machines to control and reset things like Safari preferences. Adware like Chill Tab and MyShopcoupon have been plaguing macOS users since mid-2017 through this same mechanism.
Apple Bugs
Arguably, these are becoming more common, or at least more widely publicised, as Apple pushes the limits of quality assurance in trying to keep up with its self-imposed annual update cycle. First, High Sierra and then Mojave introduced embarrassing bugs that could have given malware open season to infect and exploit macOS users.
Do You Really Need AV software on macOS?
We hope that the answer to this is self-evident by now. The built-in protections are “nice to have”, but they do not really address the complexity or sophistication of modern malware, especially when combined with Apple’s determination to rush out a minimally-tested new version of the entire OS every 12 months.
If you have endpoints running macOS, you need a security solution that does more than scan a few static signatures and prevent downloads from one or two different sources. You need a solution that has defence in-depth: a modern Next-Gen solution like SentinelOne that uses machine learning to automate detection across your entire network, regardless of whether the endpoint is running macOS, Windows or Linux.
Like this article? Follow us on LinkedIn, Twitter, YouTube or Facebook to see the content we post.